what is easiest way to hack some one else phone from your android
All-time Apps to Spy on Some other Cell Telephone - Mobile Tracker Free Download





When you lot feel abased by your wife/husband, or when you take doubts most your children'south activities or the safe of your parents, you can hack their Android phones from your calculator or mobile device to ensure their safety. No one can monitor around the clock, but there is professional spy software that can secretly monitor the activities of Android phones without making them aware.
What if y'all don't know anything about how to hack an Android phone? So you can continue reading this article.
- How to use software to hack someone'due south Android phone
- Use Google Maps to hack an Android phone from your computer
1. How to use software to hack someone'southward Android phone
Using tools such as mobile phone monitoring software, you lot don't need to carp how to hack an Android phone from your computer. It can not just rail the location of the device, but besides invade and monitor the device data. Y'all can remotely monitor more than 39 data types on the target Android device, including GPS location, messages, telephone call logs, contacts, Facebook/WhatsApp/Instagram/Line and other application data. The owner of the target device will non find the beingness of this application on the telephone. Afterward activating the monitoring mode, the phone tracking App icon in the target device will exist subconscious.
Why cull this Android phone hacker software:
- You can access this tool on Mac, Windows computer, Android device, iOS device and rails any mobile device.
- It supports nearly 6000 mobile device models from mobile telephone manufacturers such as SAMSUNG, XIAOMI, HAUWEI, Motorola, OPPO, etc.
- Through the monitoring software, y'all can crack the Instagram countersign, and also crack the communication software such as Line, Facebook, Snapchat, Skype.
- Not only can you track the online activeness of the target device, you can also set upward a geofence for information technology. When the target person leaves the surface area of the location, you will be alerted.
- Y'all do not need to root the target Android device to utilize the monitoring messages, conversations, contacts, call records, etc.
Simple steps to hack an Android phone
- Annals an account
First, click "Free Trial" and annals an account. Use your electronic mail account to create a monitoring software account. Then write down the username and password. - Complete the setup procedure
Utilize the business relationship you just created, enter the target device information, click the "Android" icon, so click "Next". - Install the application on the target Android phone__ On the target Android device, go to "Settings" and enable "Unknown Sources", so download and install the spy awarding software on the target device. After the installation is complete, start and log in to the monitoring software account, while allowing the awarding to admission the target device, and then click "Start Monitoring". The application software icon volition disappear from the target device.
- Beginning monitoring your phone
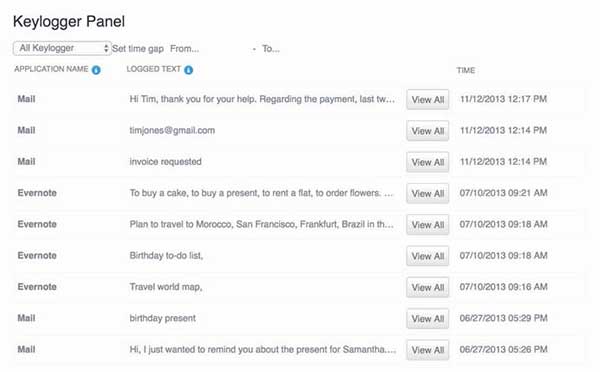
Open the browser and log in to your business relationship, click "Keylogger" on the dashboard, y'all can get the text message typed past the target user, including the lock screen password of the Android phone and other passwords. Through this method, you can hands crevice the countersign of your Android phone or tablet. You tin can also remotely monitor all data on the target Android device, such as WhatsApp letters, photos, videos, GPS locations, emails, etc.
2. Employ Google Maps to hack an Android phone from your estimator
You can also try to hack an Android phone using Google Maps. The main divergence hither is that it can simply access the location of the target Android device. Unlike monitoring software, mobile phone monitoring software, monitoring software provides a complete solution for cracking Android devices. If the GPS service is turned on, you can runway the location of the target device, you tin besides use Google Maps to view past or current moving routes, and real-time location tracking tin can also be completed. A stable network connection is required to monitor the location of the target Android device on Google Maps. Merely you need to associate the target Android device with a Google business relationship, and you need to enable location reporting and location logging and GPS.
Use Google Maps to track the location of the target Android telephone:
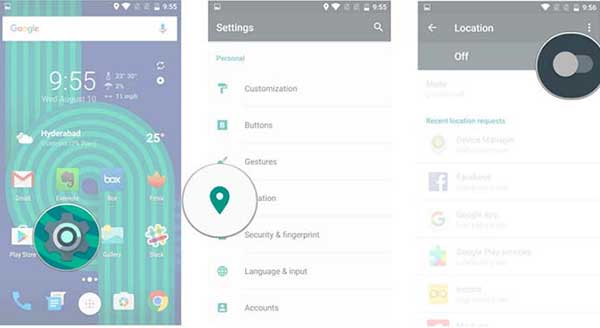
- Kickoff go to "Settings" and then turn on "Location Services" on the target Android device.
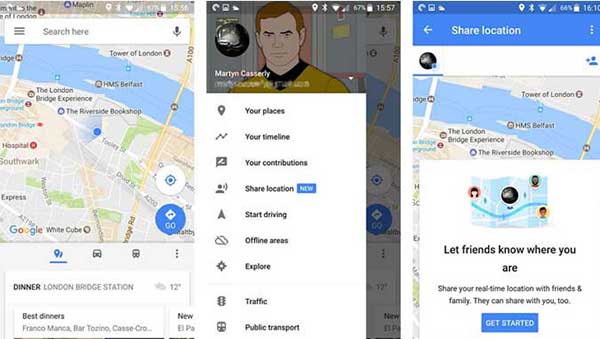
- Launch "Google Maps" and click the "Bill of fare" icon in the upper left corner of the screen.
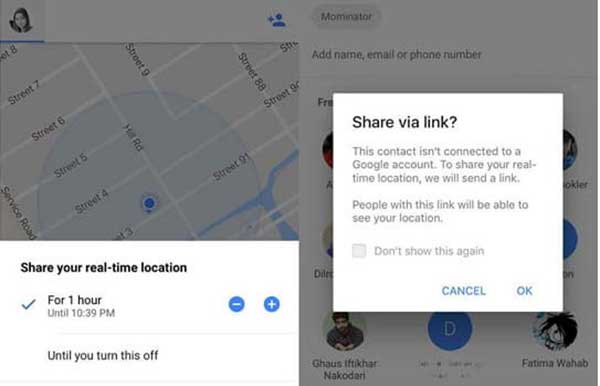
- Yous will see a popular-up window request "Share your real-time location". Select "One hour" or "Until closed", and and then press "Select Person". These contacts will be notified nigh the location of the target device. Choose your name in this list.
- If your Google account is not continued, you lot can select your number and use the "Share via connection" button on the popular-up window to share.
- You can hands track the location of the target device through your phone without any problems.
We noticed hither that when you want to hack an Android phone, there is no other style to go beyond the monitoring software. The software can not simply track real-time location, but as well remotely monitor all data of the target device. For Google Maps, you need to allow location sharing services to track the location of the device, which cannot be washed secretly. But the monitoring software mobile phone monitoring software deletes the icon of the application software, and the monitored person knows nothing nigh it.
How to avoid malicious surveillance of mobile phones
If you observe yourself e'er receiving strange, infrequently used social media messages, text messages or emails, this is a warning sign. More often than not, these softwares need to exist physically installed on the telephone first. If your phone settings change, it may exist one of the indicators of infection.
There are settings on Android devices that allow downloading and installing apps outside of the Google Store. The Root Checker plan in the Google Store tin check the root status of the telephone. You tin can select "Allow View from Unknown Sources" in the telephone settings, or check "Special Access" / "Installation Location App" to view, only there is no guarantee that it will announced on the list.
It is mostly difficult to install malware on IOS devices, but if an application called Cydia (the package manager allows users to install software packages on rooted devices) appears, information technology may indicate a problem, unless of course y'all are Downloaded software.
1. Set a countersign for your phone
Perhaps there are many friends around y'all who are likewise troublesome and refuse to set an unlocking password for the telephone. There may also exist many people who think that a simple 4-digit password tin reach the role of protecting the telephone. What I want to tell y'all is that these concepts are incorrect.
2. Employ genuine shopping App
In fact, many websites have their own apps, then try not to use browsers for shopping, because most of these companies' exclusive apps have anti-fraud features when they are designed.
iii. Sensitive Account
Don't let your phone's App or browser tape your business relationship and password. Others can log in to your account straight by opening the App while playing on your phone.
4. Turn off the automated connection to Wifi function
Plow off the automatic connectedness to Wifi function to avoid connecting to unreliable wireless networks, otherwise hackers tin can control your mobile telephone or other devices through software loopholes.
5. Turn off the Bluetooth function
Hackers can control the device through Bluetooth, and so plow information technology off when you don't need to apply the Bluetooth role.
six. Restore the telephone to manufactory settings
We often sell mobile phones we don't use, and need to reset the mobile phone to mill settings or format the SD card. We must erase the account number, password and other personal information.
7. Carefully download monitoring App software
This is not the first fourth dimension this effect has been mentioned, especially on Android devices. Many free apps spy on the user'due south address book and brusque messages and upload them to the developer, causing information leakage.
8. Articulate Internet browsing records regularly
In that location are a lot of private information in the browsing records of mobile phones, especially after opening emails, shopping online or logging in to a bank business relationship, you need to clear the history records, otherwise information technology is easy for others to hack your individual information.
9. Download remote removal software
Some remote control software, such as the iPhone mobile telephone application software Find My Phone, can not only help you lock the location of the phone and find the missing phone, just also remotely clear the personal data in the phone.
How to see other people's phone screen, telephone call history, sms, conversation, text messages, email, gps location, call recording, photos, whatsapp, messenger, facebook.The mobile spy app can remotely monitor and track my partner'southward android phone. Download spy app for complimentary and install apk file on target jail cell telephone.Best spy software - Find and locate someone's telephone online, read phone message from hubby or married woman on another prison cell telephone.
cloverbostersair1974.blogspot.com
Source: https://www.xtmove.com/how-to-hack-someones-android-phone-without-touching-it/
0 Response to "what is easiest way to hack some one else phone from your android"
Post a Comment